FedRAMP, CMMC, and Air-Gapped AI
Deploying Governance in Classified Environments
Heath Emerson, MBA — Founder & CEO
February 2026 | apotheon.ai
Download Full PDF
Get the complete whitepaper with references and citations
Executive Summary
The U.S. federal government and its defense industrial base are simultaneously navigating two converging compliance mandates: FedRAMP, which standardizes cloud security authorization for all federal agencies, and CMMC 2.0, which certifies the cybersecurity maturity of every defense contractor handling Controlled Unclassified Information (CUI) or Federal Contract Information (FCI). Both frameworks are undergoing significant modernization in 2026—FedRAMP through its 20x automation-first initiative, and CMMC through its phased rollout of mandatory third-party assessments.
At the same time, the Department of Defense and intelligence community are deploying AI systems into environments that range from commercial cloud to permanently air-gapped classified networks. This spectrum creates a fundamental engineering challenge: how do you deliver consistent AI governance across deployment environments that differ radically in their connectivity, security controls, and assessment requirements?
This paper describes how Apotheon.ai’s AIOS platform—and its THEMIS governance runtime in particular—addresses this challenge through a three-tier deployment architecture. Tier 1 (FedRAMP Cloud) deploys THEMIS as a managed service on authorized government cloud infrastructure. Tier 2 (On-Premises) installs THEMIS within customer-owned data centers for CUI boundary enforcement. Tier 3 (Air-Gapped) operates THEMIS in permanently disconnected environments with zero external connectivity, using local Hardware Security Modules and a novel dual-witness notary protocol to deliver cryptographic governance proofs that require no network connection whatsoever.
Each tier maps directly to the NIST 800-53 and 800-171 control families that underpin both FedRAMP and CMMC compliance. This paper provides that mapping, details the air-gapped evidence architecture, and offers a practical readiness assessment for organizations preparing for CMMC Phase 2 (November 2026) or pursuing FedRAMP authorization for AI-powered services.
The Converging Regulatory Landscape
FedRAMP: From Documentation to Automation
The Federal Risk and Authorization Management Program has been the government’s standardized approach to cloud security assessment since its establishment. Built on NIST SP 800-53 controls, FedRAMP defines three impact levels—Low, Moderate, and High—with increasing control counts. The FedRAMP Moderate baseline requires 325 controls; the High baseline requires 421. Authorization has historically been a documentation-intensive, multi-year process that created a significant barrier for innovative technology providers, particularly AI companies.
The FedRAMP 20x initiative, launched in early 2025, is fundamentally changing this model. Phase One tested automation-based validation with Low baseline cloud service providers, resulting in 13 authorizations through a dramatically accelerated process. Phase Two, running through March 2026, extends the same automation-first approach to Moderate baseline systems—the tier relevant to most federal AI deployments. Phase Three, planned for the second half of 2026, will formalize 20x Low and Moderate requirements for public adoption. Phase Four, expected in early 2027, will pilot the High baseline under the 20x framework.
In August 2025, GSA and FedRAMP announced prioritized authorization for AI-based cloud services, specifically enterprise-grade conversational AI engines designed for federal worker use. This AI-first prioritization, combined with 20x’s automation model, signals that FedRAMP authorization for AI governance platforms is both achievable and strategically timed for 2026.
CMMC 2.0: From Self-Attestation to Verified Compliance
The Cybersecurity Maturity Model Certification program transforms how the Department of Defense verifies contractor cybersecurity. The DFARS Final Rule, published September 10, 2025 and effective November 10, 2025, integrates CMMC requirements into the defense acquisition process through a four-phase rollout. CMMC Level 2, which applies to the vast majority of defense contractors handling CUI, requires implementation and verified compliance with all 110 security controls from NIST SP 800-171 Revision 2, organized across 14 control families.
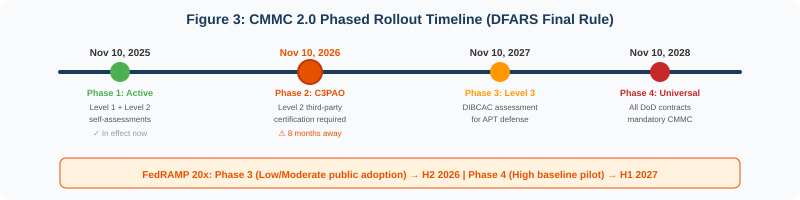
Phase 1 (active since November 2025) requires Level 1 and Level 2 self-assessments for select contracts. Phase 2, beginning November 10, 2026, introduces mandatory third-party certification assessments by C3PAOs for Level 2 contracts. Phase 3 (November 2027) adds Level 3 government-led DIBCAC assessments. Phase 4 (November 2028) makes CMMC requirements universal across all DoD contracts involving FCI or CUI.
The intersection with FedRAMP is explicit: if a DoD contractor uses a cloud service provider to store, process, or transmit CUI, that CSP must meet FedRAMP Moderate baseline requirements or demonstrate equivalent security. This means AI governance platforms serving defense contractors must either hold FedRAMP authorization or provide on-premises and air-gapped deployment options that meet or exceed those controls.
CMMC Phase 2 begins November 10, 2026—eight months from today. Organizations that have not begun preparing for C3PAO assessments are already behind. The average time from gap analysis to certification is six to twelve months.
The Air-Gapped Imperative
Defense and intelligence environments operate across a spectrum of Impact Levels (IL) defined by the DoD Cloud Computing Security Requirements Guide. IL2 covers publicly releasable information on commercial cloud. IL4 and IL5 handle CUI on dedicated government infrastructure. IL6 covers classified information up to SECRET on dedicated infrastructure that is physically and logically isolated from commercial and unclassified networks.
Air-gapped environments—networks permanently disconnected from the internet—are mandatory for IL5/IL6 classified workloads, SCIF operations, DoDIN enclaves, and programs subject to ITAR governance. These environments present unique challenges for AI systems: no cloud-based inference, no external model updates, no vendor telemetry, no cloud key management, and no network-dependent audit mechanisms. Any AI governance solution that requires external connectivity is immediately disqualified.
Major cloud providers have recognized this market. Google Distributed Cloud air-gapped provides IL6-capable infrastructure designed for permanent disconnection. Microsoft deployed air-gapped GPT-4 capabilities on Azure Government Top Secret. Oracle Cloud Isolated Regions offer fully air-gapped compute including GPU resources. Yet none of these platforms provide AI-specific governance that addresses the unique compliance requirements of agentic AI systems operating in these environments. That governance layer is what THEMIS provides.
Three-Tier Deployment Architecture
Apotheon’s AIOS platform is architected for deployment across the full spectrum of federal and defense environments. The same THEMIS governance runtime—the same policy engine, the same evidence chain, the same control enforcement—operates identically across all three tiers. What changes between tiers is not the governance logic but the infrastructure on which it runs, the key management approach, and the external anchoring mechanism.
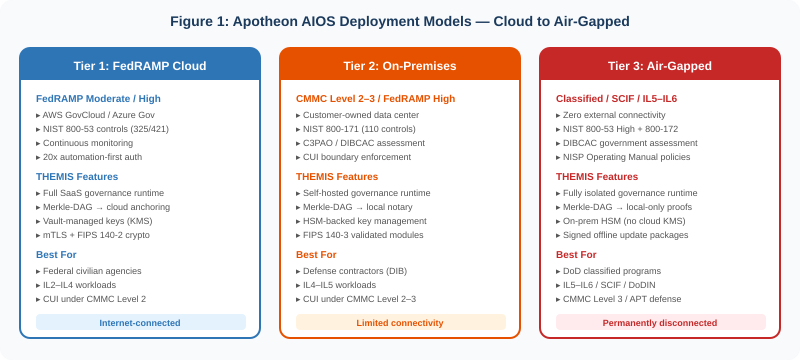
Tier 1: FedRAMP Cloud Deployment
Tier 1 deploys THEMIS as a managed governance service on FedRAMP-authorized government cloud infrastructure—AWS GovCloud, Azure Government, or GCP’s FedRAMP High environment. This tier is designed for federal civilian agencies and DoD organizations operating at IL2 through IL4, handling CUI under CMMC Level 2 with internet connectivity.
Infrastructure: Containerized THEMIS runtime on Kubernetes, deployed within the customer’s authorization boundary. All data remains within the FedRAMP-authorized region. No data crosses authorization boundaries.
Key management: AWS KMS (FIPS 140-2 Level 3 HSMs), Azure Key Vault, or GCP Cloud HSM. Customer-managed encryption keys with automated rotation. All cryptographic operations use FIPS-validated algorithms.
Evidence anchoring: Merkle-DAG root hashes are anchored to cloud-based notary services, blockchain witnesses, or RFC 3161 timestamping authorities accessible within the GovCloud environment.
Continuous monitoring: Prometheus/Grafana dashboards feed into the organization’s existing continuous monitoring infrastructure. FedRAMP’s ConMon requirements—monthly vulnerability scans, annual assessments, POA&M updates—are supported through automated reporting.
Tier 2: On-Premises Deployment
Tier 2 installs the AIOS platform within customer-owned data centers, behind the organization’s physical and network security perimeter. This tier serves defense contractors pursuing CMMC Level 2 or Level 3 certification, organizations with CUI boundary requirements, and environments operating at IL4–IL5 that maintain limited connectivity to vendor update channels.
Infrastructure: Bare-metal or virtualized THEMIS runtime on customer-owned hardware. Container orchestration via Kubernetes or direct deployment. No cloud dependencies for core governance operations.
Key management: On-premises Hardware Security Modules (HSMs)—Thales Luna, Entrust nShield, or equivalent FIPS 140-3 Level 3 validated devices. Keys never leave the HSM boundary. All signing operations occur within tamper-resistant hardware.
Evidence anchoring: Merkle-DAG root hashes are signed by the local HSM and recorded in a local notary service. If limited connectivity exists, periodic anchoring to external witnesses can supplement local proofs. If connectivity is restricted, the local notary provides standalone evidence integrity.
CUI boundary enforcement: THEMIS enforces CUI scoping boundaries at the governance layer. Agents cannot access, process, or transmit data outside the defined CUI boundary. This directly supports the CMMC scoping requirements that C3PAO assessors verify.
Tier 3: Air-Gapped Deployment
Tier 3 operates THEMIS in permanently disconnected environments with zero external connectivity. This is the most demanding deployment tier, designed for SCIF environments, DoDIN enclaves, classified programs at IL5–IL6, and any context where a single outbound connection is a compliance violation. Every component of the governance runtime—policy engine, evidence chain, key management, update mechanism—is designed to function indefinitely without network access.
Infrastructure: Fully self-contained AIOS deployment on dedicated hardware. All model inference occurs on-premises using locally hosted models. No cloud inference, no external API calls, no telemetry. The system operates identically whether the internet exists or not.
Key management: Dedicated on-premises HSMs (FIPS 140-3 Level 3). Key ceremony procedures follow NIST SP 800-57 guidance. Root keys are generated, stored, and used exclusively within the air-gapped boundary. No cloud KMS dependency.
Update mechanism: Software updates are delivered via signed offline packages on approved removable media (encrypted USB, optical media per organizational policy). Each package is cryptographically signed by Apotheon’s release authority. The THEMIS Shield Agent verifies signatures against trusted keys established during initial deployment before permitting installation. Any tampering—even a single bit—causes verification failure and blocks installation. Every update creates a complete audit trail in the Merkle-DAG.
Evidence anchoring: This is where the air-gapped deployment diverges most significantly from connected environments. Without access to external blockchain witnesses or timestamping authorities, THEMIS employs a dual-witness local notary protocol. Two authorized operators—each with independent HSM credentials—must co-sign each Merkle-DAG root hash. Neither operator alone can forge evidence. The resulting signed root provides the same tamper-evidence guarantees as external anchoring, without requiring any network connection.
In an air-gapped environment, the Merkle-DAG evidence chain plus dual-witness HSM signing provides the same mathematical tamper-evidence guarantees as cloud-anchored deployments. No external connection is required to prove that no evidence was altered, deleted, or reordered. An auditor can verify any evidence node with a portable proof bundle—no network access needed.
NIST Control Family Mapping: How THEMIS Addresses Key Requirements
Both FedRAMP and CMMC are built on NIST control frameworks—FedRAMP on NIST SP 800-53, and CMMC Level 2 on the 110 controls of NIST SP 800-171 (which are themselves derived from 800-53). The following table maps THEMIS capabilities to the NIST control families most relevant to AI governance, showing coverage across all three deployment tiers.
| NIST Family | Key Requirement | THEMIS Capability | FedRAMP | CMMC L2 |
|---|---|---|---|---|
| AC — Access Control | Least privilege, session control, remote access monitoring | RBAC/ABAC policy enforcement, agent identity verification, session-scoped permissions | AC-2 thru AC-25 | 3.1.1–3.1.22 (22 controls) |
| AU — Audit & Accountability | Audit logging, tamper protection, review/analysis/reporting | Merkle-DAG evidence chain, tamper-evident by construction, automated anomaly alerting | AU-2 thru AU-16 | 3.3.1–3.3.9 (9 controls) |
| CM — Config Management | Baseline config, change control, least functionality | Policy versioning in Merkle-DAG, immutable config history, signed update packages | CM-2 thru CM-11 | 3.4.1–3.4.9 (9 controls) |
| IA — Identification & Auth | User/device ID, authenticator management, cryptographic auth | mTLS agent-to-agent auth, HSM-backed identity, X.509 certificates | IA-2 thru IA-12 | 3.5.1–3.5.11 (11 controls) |
| IR — Incident Response | Incident handling, monitoring, reporting, testing | Automated policy violation detection, escalation workflows, evidence-backed incident reconstruction | IR-1 thru IR-10 | 3.6.1–3.6.3 (3 controls) |
| RA — Risk Assessment | Risk categorization, vulnerability scanning, risk monitoring | Continuous risk scoring, Ares adversarial testing, drift detection | RA-1 thru RA-7 | 3.11.1–3.11.3 (3 controls) |
| SC — System & Comms Protection | Boundary protection, crypto protection, CUI separation | mTLS encryption, FIPS 140-3 crypto, tenant isolation, CUI boundary enforcement | SC-1 thru SC-44 | 3.13.1–3.13.16 (16 controls) |
| SI — System & Info Integrity | Flaw remediation, malicious code protection, monitoring | Signed updates, input validation, prompt injection defense, continuous monitoring | SI-1 thru SI-16 | 3.14.1–3.14.7 (7 controls) |
| MP — Media Protection | Media access, marking, storage, sanitization | Encrypted evidence export, signed media packages, crypto-shredding for data destruction | MP-1 thru MP-8 | 3.8.1–3.8.9 (9 controls) |
| SA — Security Assessment | Control assessment, system connections, monitoring | Auto-generated compliance reports, exportable evidence bundles, continuous control effectiveness | CA-1 thru CA-9 | 3.12.1–3.12.4 (4 controls) |
This mapping is not exhaustive—NIST SP 800-171 contains 110 controls across all 14 families, and NIST SP 800-53 contains over 1,000. THEMIS addresses controls that are directly relevant to AI governance. Physical security (PE), personnel security (PS), awareness and training (AT), and maintenance (MA) remain organizational responsibilities, though THEMIS evidence can support documentation of these controls during assessment.
Air-Gapped Proofs: Cryptographic Governance Without Connectivity
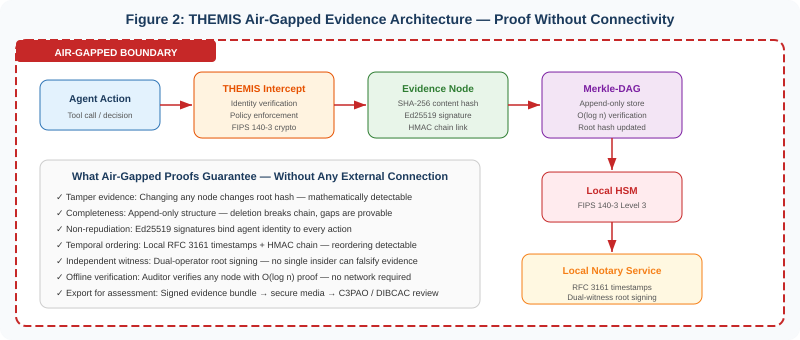
The central technical challenge of air-gapped AI governance is this: how do you prove that an AI system operated correctly—that every decision was authorized, every action was logged, and no evidence was tampered with—when you cannot rely on external witnesses, cloud services, or network-accessible timestamping authorities?
THEMIS solves this through a combination of five mechanisms that together provide the same evidentiary guarantees in a disconnected environment as cloud-anchored deployments provide in connected ones.
Mechanism 1: Content-Addressed Evidence Nodes
Every agent action generates an evidence node whose identifier (CID) is the SHA-256 hash of its contents: the action payload, the policy evaluation result, the caller identity, the timestamp, and the digital signature. This is the same mechanism used in connected deployments. The air-gapped environment changes nothing about how evidence nodes are constructed—only how they are anchored.
Mechanism 2: HMAC Chain Linking
In addition to the Merkle-DAG parent linkage, each evidence node includes an HMAC computed over the previous node’s CID using a key derived from the HSM. This creates a secondary chain that is bound to the HSM’s key material. Reordering nodes would require not just altering the Merkle-DAG structure but also recomputing the HMAC chain—which requires HSM access. Since the HSM enforces access controls and maintains its own audit log, this chain provides an additional layer of ordering integrity.
Mechanism 3: Local RFC 3161 Timestamping
THEMIS includes an embedded RFC 3161-compliant timestamping authority that runs entirely within the air-gapped boundary. The TSA’s signing key is stored in the HSM. Each evidence node receives a signed timestamp that binds the node to a specific point in time. The TSA’s clock is synchronized to a GPS-disciplined oscillator or cesium reference standard—common in SCIF environments—providing time accuracy independent of NTP or any network time source.
Mechanism 4: Dual-Witness Root Signing
This is the key innovation for air-gapped environments. At configurable intervals (every N evidence nodes, or every T minutes), THEMIS computes the current Merkle-DAG root hash and presents it to two authorized operators. Each operator authenticates to the HSM with independent credentials (smartcard + PIN, or equivalent multi-factor mechanism). Both operators must co-sign the root hash for it to be recorded as an anchor point. Neither operator alone can forge a root signature. This dual-witness protocol provides the same non-repudiation guarantee that external blockchain anchoring provides in connected deployments—without requiring any external connectivity.
Mechanism 5: Portable Proof Bundles
When an auditor (C3PAO assessor, DIBCAC reviewer, or internal compliance team) needs to verify evidence, THEMIS generates a portable proof bundle: a self-contained package that includes the evidence nodes in question, the Merkle path from each node to the nearest anchor root, the dual-witness signatures on that root, and the TSA timestamps. This bundle can be verified on any machine with the appropriate public keys—which were established during the initial deployment ceremony and distributed to authorized verifiers. No network access is required for verification. The auditor’s verification tool computes the hashes, checks the signatures, and confirms the timestamps. The entire process is offline.
The dual-witness root signing protocol means that even a fully compromised insider—with root access to the THEMIS server—cannot forge evidence without also compromising both HSM credentials. This is a stronger guarantee than most cloud-based audit systems provide, where a single cloud administrator with sufficient privileges could potentially alter log records.
CMMC 2.0 Assessment Readiness
For organizations preparing for CMMC Level 2 C3PAO assessment (mandatory from November 2026), THEMIS provides direct support for the assessment process across multiple control families. The following details what C3PAO assessors evaluate and how THEMIS helps.
System Security Plan (SSP) Support
The SSP is the core document of any CMMC assessment. It describes how the organization implements each of the 110 NIST SP 800-171 controls. THEMIS auto-generates the sections of the SSP that relate to AI governance: audit logging architecture, access control enforcement, cryptographic protection, incident response capabilities, and system integrity monitoring. These sections include architectural diagrams, control implementation descriptions, and evidence references that can be incorporated directly into the organization’s SSP.
POA&M Evidence
For controls that are not yet fully implemented, the Plan of Action and Milestones documents remediation plans. THEMIS’s Merkle-DAG provides timestamped evidence of control implementation progress—showing exactly when each control was activated, tested, and verified. This is particularly valuable because CMMC allows conditional certification if the organization achieves at least 80% compliance with a documented POA&M, provided full remediation occurs within 180 days.
SPRS Score Documentation
CMMC requires organizations to submit their compliance scores to the Supplier Performance Risk System. THEMIS’s continuous monitoring provides real-time visibility into control effectiveness, enabling organizations to maintain an accurate SPRS score. When controls drift or fail, THEMIS detects the deviation and alerts compliance teams before the gap affects the score.
Evidence for C3PAO Assessors
C3PAO assessors evaluate evidence across 320 assessment objectives. THEMIS’s evidence chain provides assessors with tamper-evident, cryptographically verifiable records of control implementation and operation. In air-gapped environments, the portable proof bundle gives assessors everything they need to verify compliance without requiring network access to the protected system.
FedRAMP 20x Alignment
The FedRAMP 20x initiative’s emphasis on automation-first, data-driven authorization aligns naturally with THEMIS’s architecture. The 20x model replaces lengthy documentation with Key Security Indicators (KSIs)—discrete, specific security tasks that can be validated automatically. THEMIS’s continuous monitoring infrastructure is designed to produce exactly this kind of evidence.
Automated control validation: THEMIS continuously monitors and reports on control effectiveness through machine-readable metrics. Encryption status, access control enforcement, audit log integrity, and incident response times are all available as real-time KSIs.
Production-sourced evidence: FedRAMP 20x Phase Two requires evidence sourced directly from production environments rather than point-in-time documentation. THEMIS’s Merkle-DAG evidence chain is, by definition, production-sourced—it records what the system actually did, not what documentation says it should do.
Continuous monitoring: FedRAMP’s ConMon requirements—monthly vulnerability scans, annual assessments, POA&M management—are supported by THEMIS’s automated reporting. The governance runtime produces the artifacts that ConMon requires without manual documentation effort.
For organizations pursuing FedRAMP authorization for AI services, the August 2025 GSA announcement prioritizing AI cloud services under 20x provides a clear pathway. THEMIS’s Tier 1 deployment is designed to operate within the FedRAMP authorization boundary, with all governance data remaining within the authorized cloud environment.
Why Air-Gapped AI Governance Is Different
Most AI governance platforms assume internet connectivity. They depend on cloud inference for model evaluation, cloud key management for cryptographic operations, vendor-hosted dashboards for monitoring, and network-accessible APIs for policy updates. In an air-gapped environment, every one of these assumptions fails.
Cloud inference dependency: Most AI tools rely on cloud-hosted inference engines. In a SCIF, this is a compliance violation. THEMIS operates with locally hosted models—any model that can run on the available hardware, whether open-source or proprietary.
Vendor telemetry: Many AI platforms quietly collect usage telemetry for analytics and model improvement. In classified environments, telemetry equals exfiltration. THEMIS collects zero telemetry. All operational data remains within the air-gapped boundary.
Cloud key management: Cloud KMS services are unavailable in disconnected environments. THEMIS uses on-premises HSMs exclusively in Tier 3, with key ceremony procedures that follow NIST SP 800-57 guidance.
Network-dependent audit: Cloud-based audit systems cannot function without connectivity. THEMIS’s Merkle-DAG evidence chain operates identically whether connected or disconnected. The math does not require a network.
Software updates: SaaS platforms update continuously. Air-gapped systems require signed offline update packages delivered via approved media channels. THEMIS’s Shield Agent verifies every update cryptographically before installation.
The common thread is sovereignty. In an air-gapped environment, the organization must have complete control over every aspect of the AI governance system—the runtime, the data, the keys, the updates, and the evidence. THEMIS is architected to provide this sovereignty at every layer.
Deployment Scenarios
Scenario 1: Defense Contractor Pursuing CMMC Level 2 (Tier 2)
A mid-size defense contractor handling CUI under multiple DoD contracts needs CMMC Level 2 C3PAO certification before November 2026. They deploy AI-powered agents for document analysis and supply chain optimization. THEMIS Tier 2 installs within their on-premises CUI boundary, enforcing access control policies on every agent action, logging all operations in the Merkle-DAG evidence chain, and generating SSP content for the 62 controls directly addressable by AI governance. When the C3PAO assessor arrives, the contractor exports a signed evidence bundle showing continuous control operation over the assessment period—not a point-in-time snapshot, but a tamper-evident record of every day’s compliance.
Scenario 2: Intelligence Community AI Program (Tier 3)
A program office deploys agentic AI systems for intelligence analysis within a SCIF environment at IL6. Zero external connectivity. THEMIS Tier 3 operates entirely within the classified boundary. Locally hosted language models perform inference on-premises. Every agent action—every document accessed, every query processed, every conclusion generated—is recorded in the Merkle-DAG with Ed25519 signatures and HMAC chain links. Dual-witness root signing occurs every 15 minutes, with two cleared operators co-signing the evidence root. When the DIBCAC assessment team evaluates the system, they receive a portable proof bundle on encrypted removable media—verifiable offline with the public keys established during the system’s initial deployment ceremony.
Scenario 3: Federal Civilian Agency on GovCloud (Tier 1)
A federal civilian agency deploys AI agents for citizen services on AWS GovCloud. They need FedRAMP Moderate compliance with their cloud environment. THEMIS Tier 1 operates as a managed service within the FedRAMP authorization boundary. Merkle-DAG evidence is anchored to cloud-based timestamping services. FIPS 140-2 encryption protects all data at rest and in transit via AWS KMS. The agency’s continuous monitoring program receives automated feeds from THEMIS’s Prometheus metrics, producing the ConMon artifacts that FedRAMP requires.
Conclusion: One Governance Runtime, Every Environment
FedRAMP and CMMC 2.0 represent the two pillars of federal and defense cybersecurity compliance for AI systems in 2026. Both are evolving rapidly—FedRAMP toward automation-first authorization, CMMC toward mandatory third-party verification. Both are built on NIST control frameworks. And both demand that organizations deploying AI systems can demonstrate, with evidence, that their systems are governed effectively.
The unique challenge for AI governance is the deployment spectrum. The same governance principles must apply whether the AI system operates on commercial GovCloud, within an on-premises CUI boundary, or inside a permanently disconnected SCIF. Most governance platforms address only one end of this spectrum. THEMIS addresses all three.
The technical foundation is the Merkle-DAG evidence chain, which provides tamper-evident, cryptographically verifiable audit records that are mathematically identical regardless of deployment environment. In connected environments, external anchoring adds independent witnesses. In air-gapped environments, the dual-witness local notary protocol provides equivalent non-repudiation through HSM-backed multi-operator signing. The proofs are portable, offline-verifiable, and assessment-ready.
For defense contractors facing the November 2026 CMMC Phase 2 deadline, THEMIS provides the AI governance layer that produces the evidence C3PAO assessors need—mapped to NIST SP 800-171 controls, documented in the SSP, and exportable as signed proof bundles. For agencies pursuing FedRAMP authorization for AI services under the 20x initiative, THEMIS’s continuous monitoring and production-sourced evidence align with the automation-first model that 20x demands. For classified programs operating at IL5–IL6, THEMIS Tier 3 delivers governance with zero external dependencies—sovereignty without compromise.
One governance runtime. Three deployment tiers. Every evidence guarantee. That is the architecture federal and defense organizations need to deploy AI with confidence in 2026 and beyond.
Learn more at apotheon.ai | Request a deployment assessment | Contact: info@apotheon.ai
References
FedRAMP (2026). Federal Risk and Authorization Management Program. fedramp.gov.
GSA (August 2025). “GSA and FedRAMP Announce Major Initiative: Prioritizing 20x Authorizations for AI Cloud Solutions.”
Secureframe (January 2026). “The FedRAMP 20x Phase Two Moderate Pilot Explained.”
Ignyte Platform (February 2026). “What New Changes Are Coming to FedRAMP in 2026?”
TrustCloud (January 2026). “FedRAMP Requirements Explained: Full 2026 Guide for Cloud Security Compliance.”
Google Cloud (February 2026). “FedRAMP Implementation Guidance on Google Cloud.”
AWS/MeriTalk (2025). “Reinventing FedRAMP in the Age of AI.”
C3 AI (December 2025). “C3 AI Achieves FedRAMP Authorization.” FedRAMP Moderate + IL5/IL6.
DoD (September 2025). DFARS CMMC Final Rule. Defense Federal Acquisition Regulation Supplement Case 2019-D041.
DoD (October 2024). 32 CFR Part 170 — CMMC Program Rule (Final Rule).
Crowell & Moring (2025). “Finally, the CMMC Final Rule: DoD Completes CMMC Rulemaking.”
Arnold & Porter (2025). “CMMC Final Rule: Key Takeaways for Defense Contractors.”
Mayer Brown (September 2025). “Department of Defense Releases Long-Anticipated Final Rule Implementing CMMC.”
Infor (2025). “Ultimate Guide to CMMC 2.0 Compliance Requirements.”
Secureframe (September 2025). “CMMC 2.0 Timeline: Key Dates & Deadlines Explained.”
Godlan (January 2026). “CMMC 2.0 Deadlines and Rules: Your Complete 2025 Compliance Guide.”
Scrut (2025). “The 14 Control Domains of CMMC 2.0 (NIST SP 800-171).”
Drata (2025). “CMMC Requirements: 2025 Compliance Standards.” 110 controls, 14 families, 320 objectives.
NIST SP 800-171 Revision 2 (2020). “Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations.”
NIST SP 800-53 Revision 5.2.0 (August 2025). “Security and Privacy Controls for Information Systems and Organizations.”
NIST SP 800-57 (2020). “Recommendation for Key Management.” Key ceremony and key lifecycle guidance.
Google Cloud (2026). “Google Distributed Cloud Air-Gapped.” IL6-capable permanently disconnected infrastructure.
Microsoft / Nextgov (May 2024). “Microsoft Deploys Air-Gapped AI for Classified Defense, Intelligence Customers.”
Oracle (2026). “Oracle Cloud Isolated Region.” Air-gapped OCI for classified workloads.
Tabnine (June 2025). “What It Really Takes to Be Air-Gapped: Inside the Architecture of Secure AI Development.”
Mattermost (August 2025). “Zero Trust in Practice: Inside Sovereign Collaboration for IL5/IL6 Missions.”
Carahsoft / Broadcom (January 2026). “Securing Air-Gapped and Classified Environments.”
Apotheon.ai (2026). THEMIS: Trusted Hash-Based Evidence Management & Integrity System. Technical Documentation.
Apotheon.ai (2026). AIOS Platform: Three-Tier Deployment Architecture. Technical Documentation.
Download Complete Whitepaper PDF
Get the full technical analysis including architecture diagrams, competitive comparison table, complete references, and implementation guidelines.