Zero-Knowledge Proofs for AI
Proving Compliance Without Revealing Sensitive Data
Heath Emerson, MBA — Founder & CEO
February 2026 | apotheon.ai
Download Full PDF
Get the complete whitepaper with references and citations
Executive Summary
In 2026, regulators no longer accept aspirational ethics statements. The EU AI Act demands operational evidence. The HIPAA Security Rule requires cryptographic safeguards. The SEC’s examination priorities place AI governance alongside cybersecurity as a top-tier concern. Organizations deploying AI agents in regulated industries face a paradox: they must prove compliance—that their systems handled data correctly, followed policy, and produced fair outputs—without revealing the sensitive data those systems process.
Zero-knowledge proofs (ZKPs) resolve this paradox mathematically. A ZKP allows one party to prove to another that a computation was performed correctly without revealing any of the inputs, outputs, or intermediate values. Applied to AI governance, this means an organization can prove to an auditor that its clinical AI agent never exposed protected health information, that its trading algorithm used only approved data sources, or that its hiring model satisfies fairness constraints—all without the auditor ever seeing patient records, trade data, or applicant information.
This paper provides an enterprise-oriented deep dive into how THEMIS, Apotheon.ai’s zero-trust governance engine, implements zk-SNARKs (zero-knowledge succinct non-interactive arguments of knowledge) as part of its cryptographic compliance framework. We explain how the technology works, why it matters for AI governance specifically, how THEMIS integrates it into real-time agent execution, and what performance characteristics enterprises can expect.
Zero-Knowledge Proofs: The Fundamentals
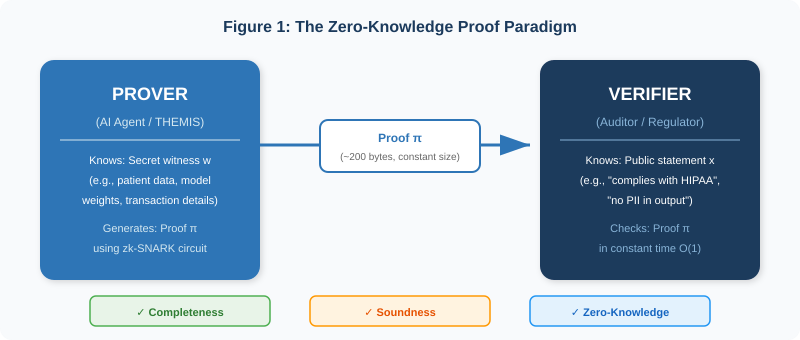
A zero-knowledge proof is a cryptographic protocol between two parties: a prover and a verifier. The prover wishes to convince the verifier that a statement is true without revealing any information beyond the truth of the statement itself. The concept was introduced by Goldwasser, Micali, and Rackoff in 1985 and has since evolved from a theoretical curiosity into production-grade infrastructure deployed across finance, healthcare, and now AI governance.
The Three Properties
Every ZKP system must satisfy three fundamental properties:
Completeness: If the statement is true and both parties follow the protocol, the verifier will always accept the proof. A legitimate prover can always convince an honest verifier.
Soundness: If the statement is false, no cheating prover can convince the verifier to accept it, except with negligible probability. A malicious actor cannot fabricate a valid proof for a false claim.
Zero-Knowledge: The verifier learns nothing beyond the truth of the statement. The proof reveals no information about the secret witness—the private data used to generate the proof. An auditor verifying that an AI system complied with HIPAA learns only that it did comply, not how the patient data was structured or what the model outputs contained.
From Interactive Proofs to zk-SNARKs
The original ZKP protocols were interactive: the prover and verifier exchanged multiple rounds of messages. For AI governance, where millions of agent actions must be verified asynchronously and potentially years after execution, interactivity is impractical. This led to the development of non-interactive zero-knowledge proofs (NIZKs) and, specifically, zk-SNARKs.
The acronym zk-SNARK encodes the key properties: Zero-Knowledge (reveals nothing beyond truth), Succinct (the proof is small and verification is fast, regardless of computation complexity), Non-interactive (a single message from prover to verifier), ARgument of Knowledge (the prover must actually “know” the witness, not just that it exists). Groth16, introduced in 2016, remains the most widely deployed zk-SNARK protocol. It produces proofs consisting of just three elliptic curve points—approximately 200 bytes—and verification requires only a single pairing computation, achievable in constant time. Empirical benchmarks show Groth16 generates proofs 68 times faster than zk-STARKs, with proofs 123 times smaller.
How zk-SNARKs Work: From Policy to Proof
Understanding how THEMIS uses zk-SNARKs requires tracing the pipeline from a human-readable governance policy to a cryptographic proof that an auditor can verify in milliseconds.
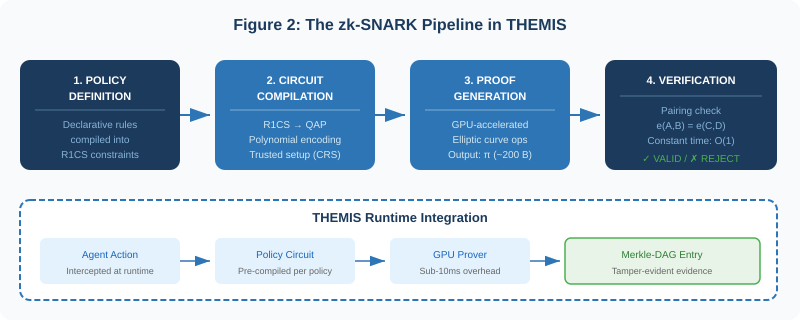
Step 1: Policy Definition as Arithmetic Circuits
THEMIS begins with declarative governance policies—human-readable rules such as “No personally identifiable information may appear in agent responses” or “All data access must be authorized by a valid session token.” These policies are compiled into arithmetic circuits: mathematical representations where every computation is expressed as addition and multiplication over a finite field.
The circuit is then converted into a Rank-1 Constraint System (R1CS)—a set of equations that constrain the relationship between inputs, outputs, and intermediate values. Each constraint takes the form A · B = C, where A, B, and C are linear combinations of variables. The R1CS captures every logical branch and comparison in the policy, ensuring that any execution satisfying all constraints provably complies with the original policy.
Step 2: Quadratic Arithmetic Programs and Trusted Setup
The R1CS is transformed into a Quadratic Arithmetic Program (QAP)—a polynomial encoding where the constraints become conditions on polynomials evaluated at specific points. This transformation is the mathematical core that enables succinct verification: instead of checking every constraint individually, the verifier checks a single polynomial identity.
Groth16 requires a one-time trusted setup ceremony that generates a Common Reference String (CRS) containing encrypted evaluation points. The security of the system depends on the assumption that at least one participant in the ceremony destroys their secret randomness. THEMIS supports multi-party computation (MPC) ceremonies where multiple independent parties contribute randomness, and publishes ceremony transcripts for verification—the same approach used by the Perpetual Powers of Tau ceremony that secures billions of dollars in blockchain transactions.
Step 3: GPU-Accelerated Proof Generation
When an agent action triggers a policy check, THEMIS’s proof generation engine takes the private witness (the actual data—patient records, transaction details, model outputs) and the public statement (the policy claim—“no PII was exposed”) and computes elliptic curve operations that produce the proof. The proof consists of three group elements on the BN128 elliptic curve, totaling approximately 200 bytes.
THEMIS’s GPU-aware proof scheduler distributes these elliptic curve multi-scalar multiplications across available GPU accelerators. Modern GPUs excel at the parallel arithmetic required for these operations, reducing proof generation times from seconds to sub-10 milliseconds for governance-scale circuits. This is critical: in a runtime governance layer, proof generation cannot introduce perceptible latency into agent execution.
Step 4: Constant-Time Verification
Verification requires checking a bilinear pairing equation: e(A, B) = e(C, D), where e is a pairing function on elliptic curve groups and A, B, C, D are derived from the proof and public inputs. This check runs in constant time—O(1) regardless of the original computation’s complexity. An auditor verifying that a clinical AI agent complied with HIPAA across 10 million patient interactions performs the same pairing check for each interaction: a few milliseconds per verification, with no access to any patient data.
THEMIS: zk-SNARKs in a Governance Runtime
THEMIS is not a standalone ZKP library. It is a governance runtime that integrates zk-SNARKs into a broader cryptographic compliance framework—alongside Merkle-DAG evidence chains, vault-based key management, and continuous control monitoring. The ZKP subsystem operates within this architecture to solve a specific problem: proving policy compliance without data exposure.
Policy Circuits as Pre-Compiled Assets
THEMIS pre-compiles each governance policy into a zk-SNARK circuit during policy deployment—not at runtime. When a policy is created or updated, the circuit compilation and trusted setup occur once, generating proving and verification keys that are stored in the policy registry. At runtime, proof generation uses these pre-computed keys, eliminating compilation latency from the hot path.
This architecture means that adding a new governance policy requires a one-time setup cost (minutes to hours, depending on circuit complexity) but imposes near-zero marginal cost on subsequent validations. Organizations can deploy hundreds of policies—covering PII detection, authorization checks, fairness constraints, data provenance verification, and output quality gates—without cumulative performance degradation.
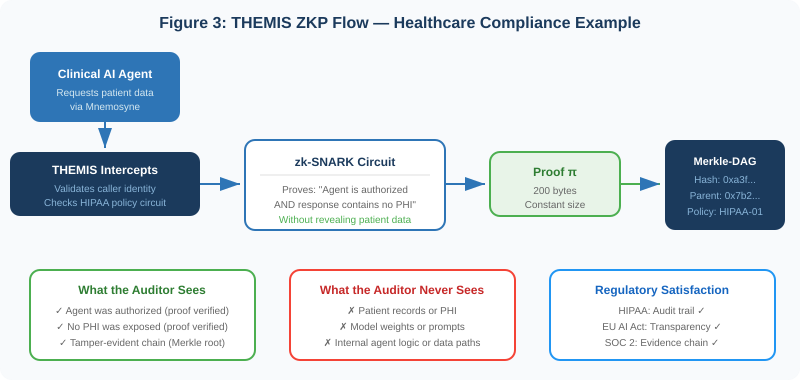
The Merkle-DAG Integration
Each zk-SNARK proof generated by THEMIS is recorded as a node in a Merkle Directed Acyclic Graph (DAG). The node contains the proof itself, a hash of the public inputs (policy ID, timestamp, caller identity), and parent hashes linking it to previous entries in the evidence chain. This creates a tamper-evident history: modifying any historical entry invalidates the hash chain from that point forward.
Periodically, THEMIS anchors the Merkle root to an external ledger—a public blockchain, an organizational audit system, or a notarization service—creating an independent timestamp that cannot be altered by either party. The combination of zk-SNARKs (proving compliance) and Merkle-DAGs (proving temporal integrity) provides what neither technology offers alone: a complete, verifiable, tamper-evident compliance record that reveals no sensitive data.
Vault Integration and Key Lifecycle
The cryptographic keys used in zk-SNARK circuits—proving keys, verification keys, and the CRS—are managed through THEMIS’s vault integration layer, supporting HashiCorp Vault, AWS KMS, Azure Key Vault, and GCP KMS. Keys remain encrypted even in memory, with decryption requiring multi-party approval. Key rotation follows organizational policy, and rotated keys are archived with their associated circuit versions to enable historical verification.
The State of ZKML: Performance, Benchmarks, and Practical Limits
Zero-Knowledge Machine Learning (ZKML) is the emerging discipline of applying ZKPs to machine learning operations. The field has progressed rapidly: proof generation overhead has decreased from 1,000,000x (2022) to approximately 10,000x (2025), with specialized systems achieving real-time performance for targeted operations.
Benchmarks and Progress
The academic and industry landscape shows accelerating capability. Daniel Kang’s research at Stanford produced the first zk-SNARK circuit for ImageNet-scale models (MobileNet v2), achieving 79% accuracy with verification in 10 seconds on commodity hardware. The EZKL library converts ONNX model files directly to zk-SNARK circuits, enabling verification of models with up to 18 million parameters. In March 2025, zkPyTorch demonstrated VGG-16 inference verification in 2.2 seconds. Lagrange’s Dynamic zk-SNARKs research, presented at the Science of Blockchain Conference 2025, introduced incremental proof updates that avoid rebuilding proofs from scratch when data changes—critical for streaming AI pipelines.
A systematic survey published in IEEE Transactions on Software Engineering (2026) identified five key ZKP protocol properties critical for AI validation: non-interactivity, transparent setup, standard representations, succinctness, and post-quantum security. The survey mapped ZKP applications across the full ML lifecycle—data preprocessing, training verification, inference verification, and online metrics—establishing a taxonomy that aligns with THEMIS’s governance scope.
What THEMIS Proves vs. What ZKML Proves
It is important to distinguish THEMIS’s governance-level proofs from full ZKML inference proofs:
THEMIS’s governance proofs are designed for hot-path enforcement: every agent action is validated in real time. Full ZKML inference proofs, while powerful for model attestation, are typically too computationally expensive for per-action enforcement and are better suited to periodic audits or dispute resolution. THEMIS supports both modes: governance proofs in the hot path, and integration with ZKML frameworks (EZKL, zkPyTorch) for batch model attestation when required by regulation.
Industry Applications: ZKPs in Regulated AI
Healthcare: HIPAA Without Exposure
A clinical AI agent recommending treatment plans must access patient histories—protected health information under HIPAA. THEMIS proves, via zk-SNARK, that the agent was authorized to access the specific record, that the response contains no PHI, and that the interaction followed the facility’s data handling policy. The auditor verifies these proofs without ever seeing the patient data. Combined with Mnemosyne’s encrypted hierarchical memory and Clio’s PII-redacting transcription, the full clinical workflow is governed end-to-end.
Financial Services: Proving Fairness Without Revealing Models
Regulators increasingly require proof that lending models do not discriminate based on protected characteristics. THEMIS can prove, via zk-SNARK, that a model’s decision process satisfies fairness constraints (e.g., demographic parity or equalized odds) without revealing the model’s weights, the applicant’s data, or the specific decision boundary. This addresses both SEC audit requirements and competitive concerns about model IP exposure.
Defense and Intelligence: Classified Correctness
Government AI systems processing classified information cannot expose data to external auditors—yet must demonstrate compliance with policy. THEMIS’s zero-knowledge architecture was designed for exactly this constraint: proofs can be verified by cleared or uncleared personnel alike, since the verification process reveals nothing about the classified inputs. Air-gapped deployment with multi-party key management ensures that even the governance infrastructure operates within classification boundaries.
Cross-Border Compliance: GDPR Data Sovereignty
GDPR requires that personal data of EU residents remain within approved jurisdictions. When AI agents process data across federated deployments, THEMIS proves that data residency requirements were satisfied without requiring the auditor to access the actual data or inspect cross-border transfer logs. The proof attests to the property (data stayed within EU boundaries) without revealing the data itself.
Challenges, Limitations, and the Road Ahead
Trusted Setup
Groth16’s requirement for a per-circuit trusted setup introduces both operational complexity and a theoretical trust assumption. THEMIS mitigates this through multi-party computation ceremonies and published transcripts, but organizations must understand that the security of each circuit depends on at least one ceremony participant having destroyed their randomness. For organizations uncomfortable with this trust model, THEMIS’s roadmap includes support for transparent setup schemes (e.g., PLONK with universal SRS, or Spartan) that eliminate the per-circuit ceremony entirely.
Circuit Complexity Scaling
As governance policies grow more complex—incorporating multi-step authorization chains, cross-model fairness checks, or temporal data flow constraints—the resulting arithmetic circuits grow proportionally. While THEMIS’s GPU acceleration handles current governance circuits comfortably, extremely complex policies may require circuit optimization techniques such as recursive proof composition (folding), where multiple proofs are combined into a single accumulator proof. Research from Lagrange on dynamic zk-SNARKs and the Nova/SuperNova folding schemes points toward production viability for these approaches by late 2026.
Post-Quantum Security
Current zk-SNARKs rely on the hardness of the discrete logarithm problem on elliptic curves—a problem that quantum computers could theoretically solve. While practical quantum attacks remain years away, organizations with long compliance horizons (defense, healthcare records, financial archives) should plan for post-quantum transitions. THEMIS’s pluggable proof backend is designed to swap underlying cryptographic primitives without changing the policy interface, enabling migration to lattice-based or hash-based ZKP schemes as they mature.
The ZKML Convergence
The long-term trajectory is clear: governance proofs and inference proofs will converge. As ZKML performance improves—from the 10,000x overhead of 2025 toward the sub-100x overhead that hardware acceleration and folding schemes promise—organizations will be able to prove not just that policies were followed, but that the exact declared model produced the exact output, all in a single cryptographic attestation. THEMIS is architected for this convergence, with a proof backend that can incorporate full ZKML circuits alongside governance circuits as the technology matures.
The future of AI compliance is mathematical, not procedural. Zero-knowledge proofs transform governance from a documentation exercise into a cryptographic guarantee—provable, tamper-evident, and privacy-preserving by construction.
Conclusion
Zero-knowledge proofs represent a fundamental advance in how organizations can demonstrate AI compliance. Instead of exposing sensitive data to auditors, generating reams of documentation, or relying on trust in vendor-controlled logging systems, organizations can produce compact cryptographic proofs that any verifier can check in milliseconds—proofs that reveal nothing beyond the truth of the compliance claim.
THEMIS operationalizes this technology as part of a complete governance runtime. Its pre-compiled policy circuits, GPU-accelerated proof generation, Merkle-DAG evidence chains, and vault-managed key infrastructure provide the full stack required to deploy zk-SNARKs in enterprise AI systems—not as a research experiment, but as production infrastructure that intercepts every agent action and produces verifiable evidence of compliance.
For organizations in healthcare, financial services, defense, and government—where the stakes of AI governance failures are measured in regulatory fines, patient safety, and national security—THEMIS offers something no other governance platform provides: mathematical proof that your AI systems behave as claimed, without ever revealing the sensitive data they process.
In a regulatory environment that increasingly demands operational evidence rather than aspirational statements, zero-knowledge proofs are not a feature. They are the foundation.
Learn more at apotheon.ai | Request a demo of THEMIS
References
Goldwasser, S., Micali, S., & Rackoff, C. (1985). “The Knowledge Complexity of Interactive Proof-Systems.” STOC ’85.
Groth, J. (2016). “On the Size of Pairing-Based Non-Interactive Arguments.” EUROCRYPT 2016. Lecture Notes in Computer Science, vol 9666.
Scaramuzza, F. & Tamburri, D. A. (2025/2026). “Zero-Knowledge Proofs for AI Validation and Verification.” IEEE Transactions on Software Engineering. arXiv:2505.20136.
Sherburn, E. et al. (2025). “A Framework for Cryptographic Verifiability of End-to-End AI Pipelines.” ACM IWSPA ’25.
Awathare, N. et al. (2025). “A Comparative Analysis of zk-SNARKs and zk-STARKs: Theory and Practice.” arXiv:2512.10020.
Kang, D. et al. (2022). “Trustless Verification of Machine Learning.” Stanford University. Preprint.
South, T. et al. (2024). “Verifiable Evaluations of Machine Learning Models Using zkSNARKs.” arXiv:2402.02675.
Lagrange Labs (2025). “Dynamic zk-SNARKs.” Science of Blockchain Conference 2025.
EZKL / zkonduit (2024–2025). “EZKL: Easy Zero-Knowledge Inference.” Open-source library. github.com/zkonduit/ezkl.
Peng, J. et al. (2024). “ZKML Survey: Zero-Knowledge Machine Learning.” Comprehensive survey covering 2017–2024.
ICME Research (2025). “The Definitive Guide to ZKML (2025).” Blog.icme.io.
Kudelski Security (2025). “ZKML: Verifiable Machine Learning using Zero-Knowledge Proof.” Technical Analysis.
Fowler, G. A. (2025). “Trust, But Verify: Verifiable AI and the Dawn of ZKML.” Medium.
Calibraint (2025). “Zero Knowledge Proof AI in 2026: Secure, Breakthrough Verifiable AI.”
Apart Research (2026). “The Technical AI Governance Challenge.” Hackathon Brief.
European Union (2024). EU Artificial Intelligence Act. Regulation (EU) 2024/1689.
HHS Office for Civil Rights (January 2025). Proposed HIPAA Security Rule Update.
SEC (November 2025). 2026 Examination Priorities: AI Governance and Cybersecurity.
Gartner, Inc. (June 2025). “Gartner Predicts Over 40% of Agentic AI Projects Will Be Canceled by End of 2027.”
Gravitee (February 2026). “State of AI Agent Security 2026 Report.” Survey of 900+ Executives.
Apotheon.ai (2026). THEMIS: Trusted Hash-Based Evidence Management & Integrity System. Internal Technical Documentation.
Download Complete Whitepaper PDF
Get the full technical analysis including architecture diagrams, competitive comparison table, complete references, and implementation guidelines.